Previous parts:
In December 2014, Der Spiegel published a major investigation into NSA and GCHQ's systematic efforts to break internet encryption. The article was accompanied by a large batch of technical documents covering VPN exploitation tools, SSL/TLS decryption programmes, and internal training materials. The reporting described how the agencies had cracked VPN connections used by airlines, telecommunications firms and government networks, and explained the broader infrastructure NSA had built to undermine encryption at scale.
Buried in one of those training documents is something the article did not mention: evidence that NSA had obtained router configuration files from the network infrastructure of the United Nations Assistance Mission for Iraq (UNAMI).
The document in question is a VPN signals development training presentation produced by NSA's OTTERCREEK team (division S31244), titled "VPN SigDev Basics." Der Spiegel published it under the German title Präsentation, die die Entwicklung von Angriffstechniken auf VPN behandelt ("Presentation on the development of attack techniques against VPN"). The document's purpose is to teach NSA analysts how to find, assess and exploit VPN connections used by targets of interest, using real operational data to illustrate the tools.
One of those tools is DISCOROUTE, a component of NSA's Network Knowledge Base. It is a database of router configuration files collected from target networks through two methods: passive interception of network management traffic, and active hacking operations conducted by TAO. When an analyst wants to know how a target network is configured, what encryption it uses, what pre-shared keys protect its VPNs, or what other systems it connects to, DISCOROUTE is one of the primary tools available to them.
DISCOROUTE and the UNAMI routers
The presentation includes a screenshot of an analyst running a free-text search for "UNAMI" across the entire DISCOROUTE database, with no date or country filters applied, but with the "Crypto Keys" manifest filter checked, meaning the search was specifically configured to surface only UNAMI routers whose captured configuration files contained cryptographic key material. The screenshot shows 'eleven results, though the pagination indicates there were more.
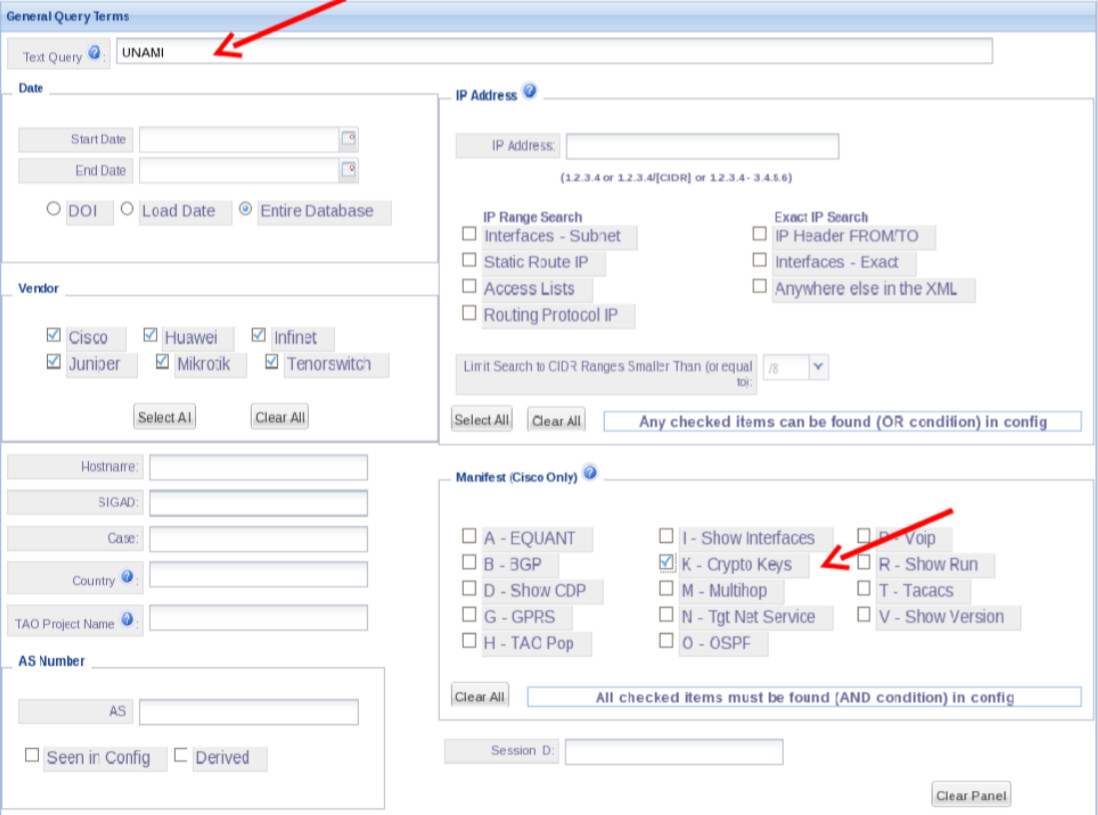
The DISCOROUTE 'UNAMI' query. Arrows are present in the original document.
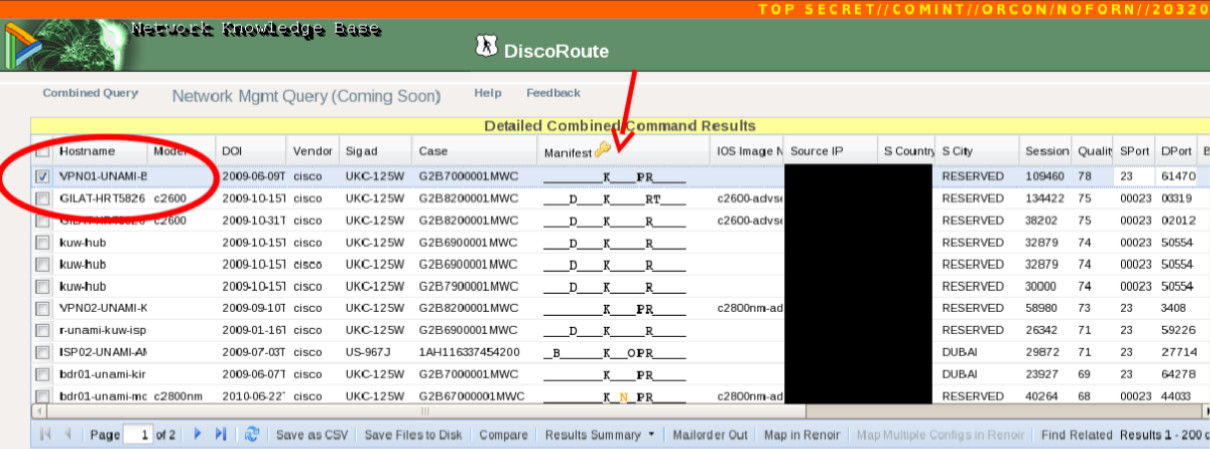
The results returned by the DISCOROUTE query. Eleven routers associated with UNAMI infrastructure are visible. Ten were collected from UKC-125W, a UK-designated collection point. One, ISP02-UNAMI-AM, was collected from US-967J, identified in a separate published NSA document as the Special Collection Service station in Kuwait City, at the time operating a FORNSAT system targeting Iranian satellite communications. Circle and arrows are present in the original document.
UNAMI is the United Nations Assistance Mission for Iraq, a special political mission established by UN Security Council Resolution 1500 in 2003. At the time these router configurations were collected (2009), UNAMI operated across Iraq and maintained a significant presence in Kuwait, which served as a logistics hub for the mission.
The hostnames visible in the results table are unambiguous:
- VPN01-UNAMI-B
- VPN02-UNAMI-K
- kuw-hub
- r-unami-kuw-isp
- GILAT-HRT5826
- bdr01-unami-kir
- bdr01-unami-mc
- ISP02-UNAMI-AM
The "kuw" prefix appearing in multiple hostnames, kuw-hub and r-unami-kuw-isp, strongly suggests Kuwait. One entry, ISP02-UNAMI-AM, shows DUBAI in the city column, suggesting routing through the UAE. One hostname, GILAT-HRT5826, likely refers to equipment from Gilat Satellite Networks, an Israeli VSAT provider.
The payload visible in the screenshot confirms this is not simply metadata. NSA had obtained the actual router configuration files. The banner text on one router is visible:
UNAMI If you do not have explicit authorization issued by UNAMI NMU to access this device, leave now! THIS ROUTER IS THE VOICE GATEWAY INTENDED FOR USE WITH THE ████████
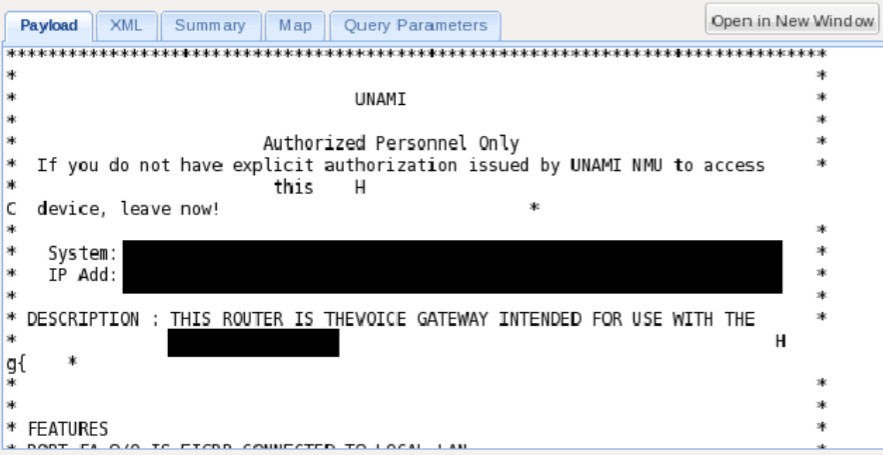
This strongly indicates that NSA had visibility into UNAMI's voice communications infrastructure as well as its data network.
DISCOROUTE collects router configurations through passive interception of network management sessions and active hacking. The training document states this explicitly. For a router to appear in DISCOROUTE with its full configuration visible, NSA either intercepted the configuration during transmission or actively broke into the device. In either case, NSA had access to the internal network architecture, VPN configurations, and likely the credentials protecting UNAMI's communications infrastructure.
The explicitly named query, "UNAMI," means this was not incidental collection. The query returned results across multiple routers in multiple locations. Someone at NSA was specifically looking for UNAMI infrastructure, and their surveillance database had answers.
NSA surveillance of diplomatic institutions is not new. In August 2013, Der Spiegel reported on systematic NSA surveillance of the EU, IAEA and UN, based on classified documents the journalists had seen but did not publish. The reporting described how NSA infiltrated the UN's internal computer network, planted bugs in EU diplomatic offices, and broke into the UN's videoconferencing system in New York, with the agency describing the last accomplishment in its own documents as "This traffic is getting us internal UN VTCs (yay!)." The reporting was explicit that the surveillance "has little or nothing to do with counter-terrorism."
Why this went unreported
The most likely explanation is the same one that applies to many unreported details in the published Snowden documents: the finding is buried in screenshots, within a large batch of technical documents, accompanying a story focused on a different subject. Der Spiegel's December 2014 encryption article was about SSL/TLS breaking, VPN decryption programmes, and the BULLRUN initiative. The VPN SigDev training document was one of many published alongside it. People reading that story would have little reason to scrutinise every screenshot in a training presentation.
To our knowledge, no reporting has previously identified or discussed the UNAMI router data visible in this document. The August 2013 reporting relied on documents Der Spiegel saw but did not publish. This document is published. And where the 2013 story concerned UN headquarters communications, this shows something more granular: actual router configuration files, with cryptographic key material, from the operational network of a UN field mission stored in a database designed for one purpose, exploiting routers and VPNs.